How can you move beyond the limitations of BI and traditional tools (Excel) to truly transform your...
Purchase-to-Pay (P2P) Process Controls: Continuous Fraud Detection and Monitoring with Eye2Scan
The Purchase-to-Pay (P2P) process, also known as Procure-to-Pay, includes all steps from identifying procurement needs through final payment. Ensuring a smooth and secure P2P process is essential for organizations, but this process is often vulnerable to procurement fraud, as highlighted by the French Anti-Corruption Agency (AFA) in its anti-fraud accounting control guide.
According to the ACFE Annual Report : Report to the Nation 2024, procurement is among the top five departments with the highest median fraud losses. The P2P process, with its complex interactions, systems, stakeholders, and financial flows, presents a heightened fraud risk. While internal controls help reduce this risk, conducting periodic checks can be time-consuming and inefficient.
IImagine an advanced tool that provides real-time fraud detection across every stage of P2P—filtering out false positives and focusing your attention on genuine fraud risks. Eye2Scan is that solution. This powerful tool applies data analytics and automated controls to the P2P process, from purchase requests to payments, delivering comprehensive and proactive fraud detection.
Automated P2P Controls with Eye2Scan: Key Examples
Examinons quelques exemples, parmi d’autres, d’utilisation d’Eye2Scan pour identifier les risques de fraude à chacune des 5 étapes clés du processus P2P :
 Purchase Request (1)
Purchase Request (1)
The P2P process begins with identifying goods or services needed and issuing a purchase request. Eye2Scan checks compliance by verifying that each order is preceded by an approved purchase request. Orders placed without a request are flagged as potential fraud.
Purchase Order (2)
Upon approval, a purchase order initiates procurement. Eye2Scan compares each purchase order to the corresponding request, detecting price or quantity discrepancies and any unauthorized changes.
Goods Receipt(3)
When suppliers deliver goods or services, a receipt is generated. This step ensures that the received goods, whether partial or complete, match the purchase order. Eye2Scan actively monitors orders lacking a prior receipt, as this could indicate potential fraud.
Invoicing (4)
Suppliers issue invoices that need to be reconciled with purchase orders and receipts in a three-way matching process. This essential step validates quantities, prices, as well as legal and banking information. Eye2Scan checks that payment terms on invoices align precisely with negotiated supplier terms, automatically identifies invoices not linked to an order (highlighting high-risk cases), and detects duplicate accounting entries. With well-configured management rules, Eye2Scan also enables companies to create an exception list for officially authorized “derogatory” flows, focusing investigations on genuinely suspicious cases.
Paiement (5)
Eye2Scan monitors supplier payments to ensure they comply with contract terms, highlighting any direct account transactions that bypass sub-ledger accounting—a key anti-fraud control under FCPA or France’s Sapin II law..
Segregation of Duties
.png?width=384&height=235&name=ERP%20%20Data%20Lake%20(2).png) Segregation of duties is essential to prevent internal fraud within the P2P process, ensuring that different individuals handle distinct steps to reduce collusion risk. Eye2Scan continuously and automatically verifies that duties are appropriately separated, monitoring segregation of duties (SoD) for each transaction. It ensures that no single individual performs multiple critical steps in the P2P process, particularly between ordering and receiving, especially if user profiles are not “perfectly” managed and maintained.
Segregation of duties is essential to prevent internal fraud within the P2P process, ensuring that different individuals handle distinct steps to reduce collusion risk. Eye2Scan continuously and automatically verifies that duties are appropriately separated, monitoring segregation of duties (SoD) for each transaction. It ensures that no single individual performs multiple critical steps in the P2P process, particularly between ordering and receiving, especially if user profiles are not “perfectly” managed and maintained.
Tracking Identified Anomalies in the Purchase-to-Pay (P2P) Process Through to Resolution
Identifying anomalies in the P2P process is crucial, but what happens next? How can we deepen the analysis and involve key stakeholders at each stage of the procurement process to determine if there’s a real issue?
Eye2Scan enables organizations to convert detected anomalies into alerts that notify process managers directly. These managers can log into the Eye2Scan platform to add comments, attach supporting documents, and complete verification checklists, such as, “Was the purchase order received?” or “Was the purchase order validated by the responsible person?” Supervisors can then review these responses, assign a status to each anomaly, and conduct further follow-up if needed.
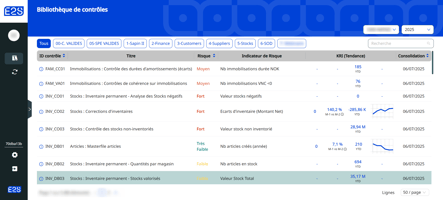
A centralized dashboard consolidates audit control campaigns and continuous P2P monitoring across different entities, providing real-time updates on anomaly statuses. This setup standardizes controls across the organization, giving internal auditors and controllers a comprehensive, unified view.

Continuous Internal Controls for the P2P Process
Once the right P2P controls are established with appropriate business rules, they operate continuously, delivering up-to-date results at your preferred frequency. This ongoing monitoring allows you to identify anomalies in real-time, boost productivity, and take a more proactive approach to risk management. By integrating the results from various controls, you’ll be able to anticipate potential risks and make well-informed decisions. If you’re interested in learning more, we would be delighted to provide a personalized demonstration.
With Eye2Scan, organizations benefit from constant, proactive monitoring of the entire P2P process, detecting anomalies and suspicious activities as soon as they appear. This proactive approach helps companies reduce fraud risk, improve operational efficiency, strengthen trust in procurement integrity, and enhance compliance.

.png?height=200&name=Global%20Internal%20Audit%20Standards%20IIA%20(6).png)